We’re frequently asked how to enable compliance notifications for devices enrolled in Microsoft Intune. Although this task isn’t difficult, there are numerous ways to easily misconfigure it.
The basic requirements are straightforward. You’ll need an Entra (formerly Azure AD) tenant with users that are licensed for Intune (either directly or as part of another license such as Enterprise Mobility + Security), as well as for Entra ID Premium. In addition, your Mobile Device Management (MDM) authority must be set to Intune. Once those requirements are met, you need to consider three areas of configuration: policy assignment, non-compliance notifications, and policy configuration.
Policy Assignment
Each compliance policy must be assigned to either All Users in a directory or to a security group that contains users. This group can be synchronized from your onsite AD via Entra ID Connect (source type Windows Server AD) or it can be an Entra group (source type Cloud). The devices used by the users contained in the security group will be evaluated for compliance.
Non-Compliance Notifications
Two actions are available once a device is deemed noncompliant.
- The default action, which immediately marks the device as noncompliant. You can customize how long it takes a device to be deemed noncompliant.
- Notification email messages based on configured templates are sent to the end user.
Notifications are simple message templates that can be emailed to a user when his or her device is deemed noncompliant.
At this time, you cannot use variables to replace text or include exact errors. This means that if you have a policy that will set a device as noncompliant for being rooted, unencrypted, and having an OS version greater than a specific value, the notification needs to state all three of these parameters if you want to provide detailed information.
Having a notification that exactly matches the policy details will provide a much clearer picture for your users when they receive a non-compliance email message. You can include a generic statement and a link to your company’s mobile device management web portal, where the compliance failures can be itemized. However, utilizing a personalized and concise email message can reduce the number of calls or complaints from users who are worried that the email message is a scam.
When you create a new notification, you must complete three fields:
- Name: This name is used only for the notification management
- Subject: The subject of the email to be sent
- Message: The message body to be sent
The other three options can be enabled or disabled as desired.
Policy Configuration
Once the assignment type and notifications are determined or configured, you can create the actual policy. When configuring the policy properties, select the option that allows you to configure the Actions for noncompliance setting.
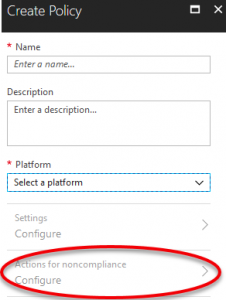
As mentioned earlier, the default action is for a device to be immediately marked noncompliant upon compliance policy failure. If you need to change this setting, select the action to change the schedule from the default value of 0 (immediately) to any number of days.
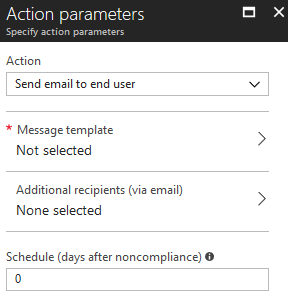
To add an email notification to the Actions for noncompliance setting, select the Add option. The only action available is Send email to end user.
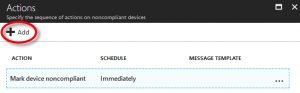
Selecting Message template will allow you to choose one of the notifications that you created in the previous section. Additional recipients are configurable but must be contained within an email-enabled Entra group to be selected. Lastly, you can modify the schedule for when the email is sent.
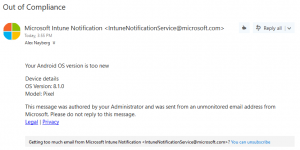
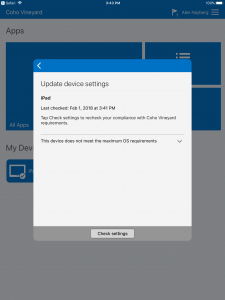
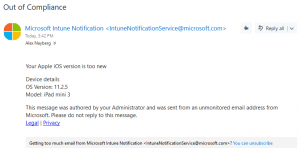
Applying a compliance policy to an Apple iOS-based device if the device’s iOS version is newer than the compliance policy permits will result in the device failing its compliance verification. Due to the notification settings, the end user will receive an email notification (preconfigured in the compliance policy) as shown below.
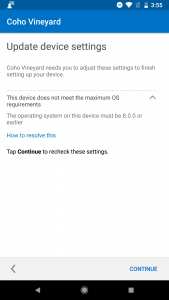
Likewise, applying a compliance policy to an Android-based device to prevent a newer Android OS than permitted will result in a similar error message on the device, as well as an email notification.